phpMyFAQ Stored HTML Injection at contentLink
Moderate severity
GitHub Reviewed
Published
Mar 25, 2024
in
thorsten/phpMyFAQ
•
Updated Mar 25, 2024
Description
Published by the National Vulnerability Database
Mar 25, 2024
Published to the GitHub Advisory Database
Mar 25, 2024
Reviewed
Mar 25, 2024
Last updated
Mar 25, 2024
Summary
Due to insufficient validation on the
contentLinkparameter, it is possible for unauthenticated users to inject HTML code to the page which might affect other users. Also, requires that adding new FAQs is allowed for guests and that the admin doesn't check the content of a newly added FAQ.PoC
Browse to ../phpmyfaq/index.php?action=add&cat=0 , enter
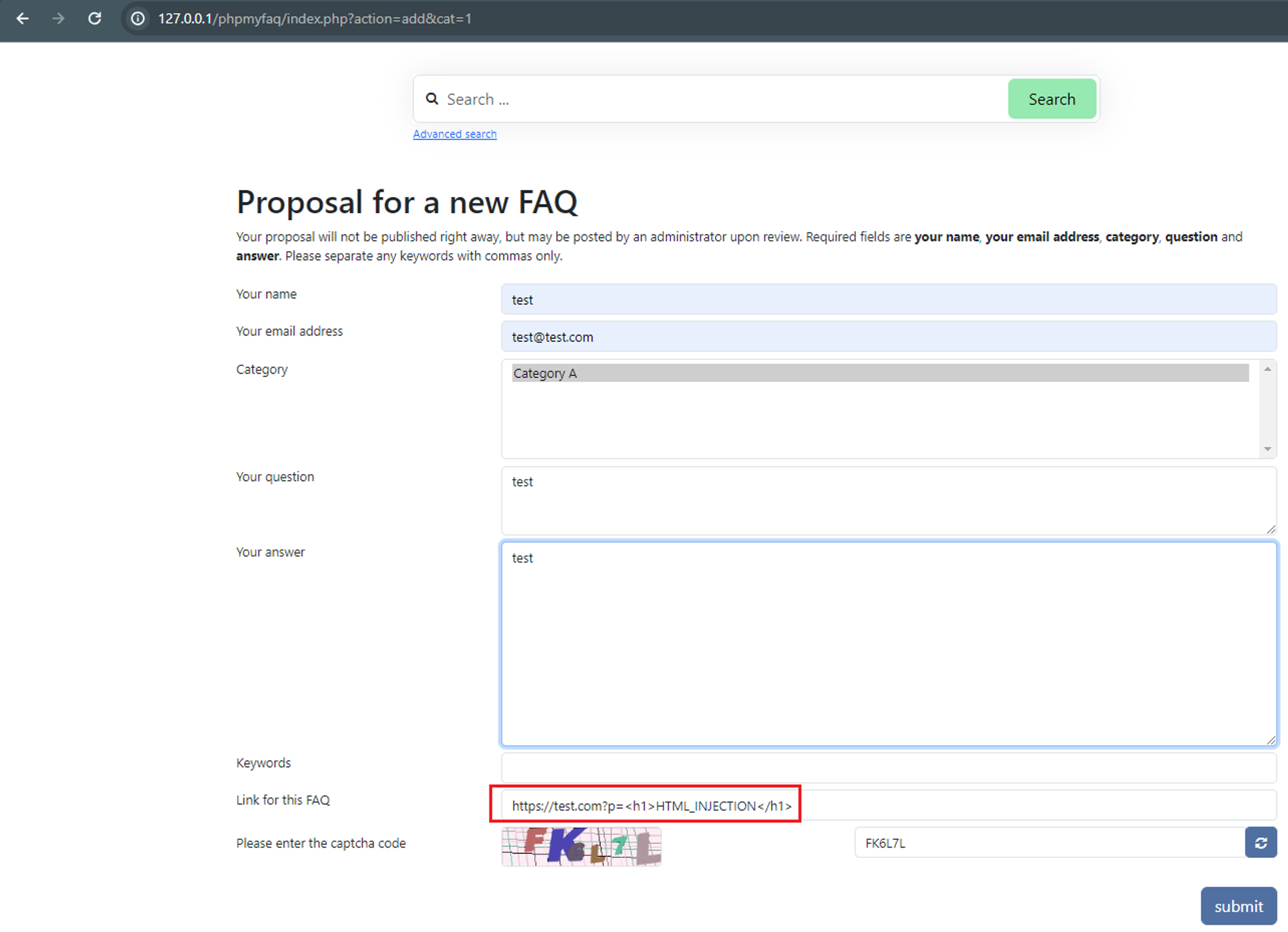
https://test.com?p=<h1>HTML_INJECTION</h1>for the contentLink parameter.Verify the HTML injection by viewing the FAQ itself, “All categories” → “CategoryName” → ”QuestionName”.
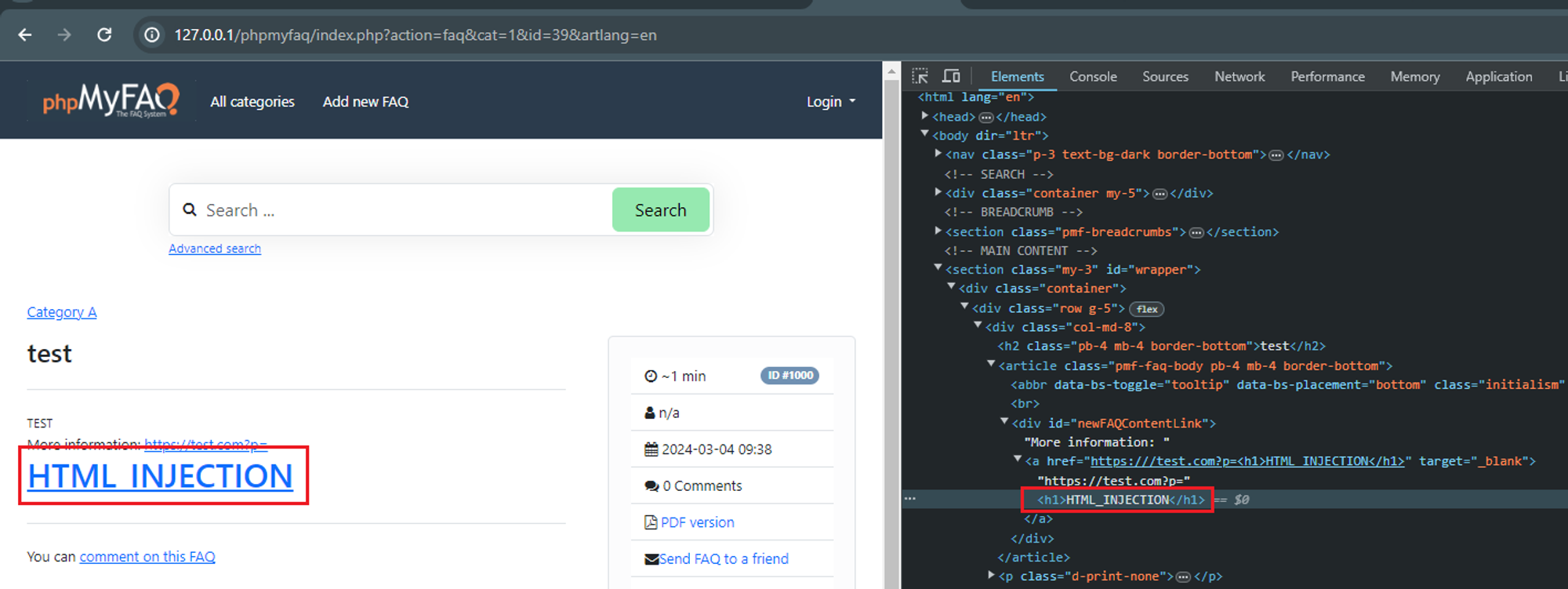
Impact
Attackers can manipulate the appearance and functionality of web pages by injecting malicious HTML code. This can lead to various undesirable outcomes, such as defacing the website, redirecting users to malicious sites, or altering the content to deceive users. Additionally, unauthenticated HTML injection can compromise user privacy by displaying sensitive information or misleading content. It undermines the integrity of the application and erodes user trust, potentially resulting in loss of reputation and credibility.
References